Tech Stack and Workflows - Today
The Modern Duty Belt, pt. 1
Hi,
Welcome to Roll Call, a newsletter about the state of policy and technology in public safety, and the people shaping it. If you’d like to sign up, you can do so here. Or just read on…
It’s been a while! There are too many exciting topics in public safety, and I’ve spread myself too thin over the last weeks. Shipping work, even if it’s not as complete as it could be, has to be more of a focus. Going forward, expect a faster cadence of one-take posts. Over time the connections between them will grow stronger and a theory of what we’re building to should become clear. Some things that I’m working on:
A better way of doing a weekly wrap on policies and technologies that are in flux. The foundation is a list of major police departments and sheriff’s offices. To ensure most Major City Chiefs and Major County Sheriffs are represented, it will include somewhere around 200 agencies. Some agencies are more important than others when it comes to developing policies that are copied across the country. On top of that, it’s not always the same governing body developing those policies; it can be the city council, the mayor, the sheriff, the police union, the district attorney, or another regulatory body. After mapping this network, there will be regular, automated updates sent out about which departments are reacting to what policy/tech developments.
A deep look into what the tech stack looks like at major agencies. Today’s note will introduce the concept, but it will grow into a valuable series examining how much agencies are spending on which tools, both software and hardware.
A series of interviews with leaders in public safety ranging from technology executives to crime analysts, chiefs to historians, policy makers to union officials, and everyone in between. I have 5 recorded, and a few more scheduled. If you know anyone whose viewpoint is vital to understanding where public safety is going over the next 25 years, please introduce me (mitchell@rollcall.media).
An analysis of recruiting in law enforcement; why is it so difficult, where do most recruits come from, how might agencies adapt?
Today I’m outlining the tech stack that public safety workflows operate on. There are three goals in writing this: first, it should give us a common vocabulary when looking at the companies that make up the value chain. Second, as someone who came from outside public safety, it took me probably 6 months to wrap my head around the basic workflows and tools used in law enforcement. I hope this can serve as an introduction for laypeople in understanding the complexity of mission critical systems. Third, it’s possible this sparks some bright people to think about starting ventures that address the complexities in public safety without simply adding tools but by addressing the jobs to be done in keeping neighbors safe.
Let’s start at the very beginning. At a high level, what does the lifecycle of a call for service look like?
Lifecycle of a CFS

The call for service (CFS) is initiated. Most often, this is someone calling 911.
That call is directed to a public safety answering point (PSAP). The location, urgency, and appropriate response type is determined. Responders are dispatched.
Units arrive on scene. They decide if and how to react to a current or past incident.
If the incident is a crime, there is an investigation. An investigation can take place while the incident is occurring (robbery in progress) and/or after.
A suspect is arrested and brought into custody.
A suspect is booked into a holding cell or jail until trial/sentencing.
The suspect goes to court, is sentenced, and is released or sent to prison.
Involved Roles
Before slotting first responders into the CFS lifecycle, it’ll be helpful to define the actors involved. Public safety is a fairly small sector. In 2019, there were an estimated 2.25 million full time employees. The outlook for the sector is above the national average for job growth, with corrections being a notable exception.


Who’s involved?
Dispatch / 911 Call Takers / Telecommunication Officers: These folks arguably wear the most hats in public safety. I would say most underrated, but they claim to be underrated so often maybe they’re appropriately rated. Have to understand the location and nature of a CFS, dispatch the right team to the scene, and relay all pertinent information to the team while the incident is in progress. They generally work in a PSAP.
Law Enforcement: Police officers, sheriff’s deputies, and state troopers. Are the default response to most valid CFS. Made up of sworn (70% of LE) and civilian (30%) employees. Includes investigations and detectives, who are sworn.
Firefighters: Respond to fires. Fight them. Made up of sworn (35% of FF) and volunteer or civilian (65%) staff.
Emergency Medical: Respond to medical emergencies. Emergency medical technicians (EMTs) and paramedics. Are usually attached to the fire department or cross-functional employees.
Legal: Prosecute on behalf of the state/county/city, and defend suspects unable to pay (indigent) in legal matters. Made up of prosecutors and public defenders. Mostly organized at the state and county levels, although some major cities have city prosecutors.
Corrections: Work in federal, state, or county prisons.
Alright, now let’s overlay the CFS lifecycle with these roles.
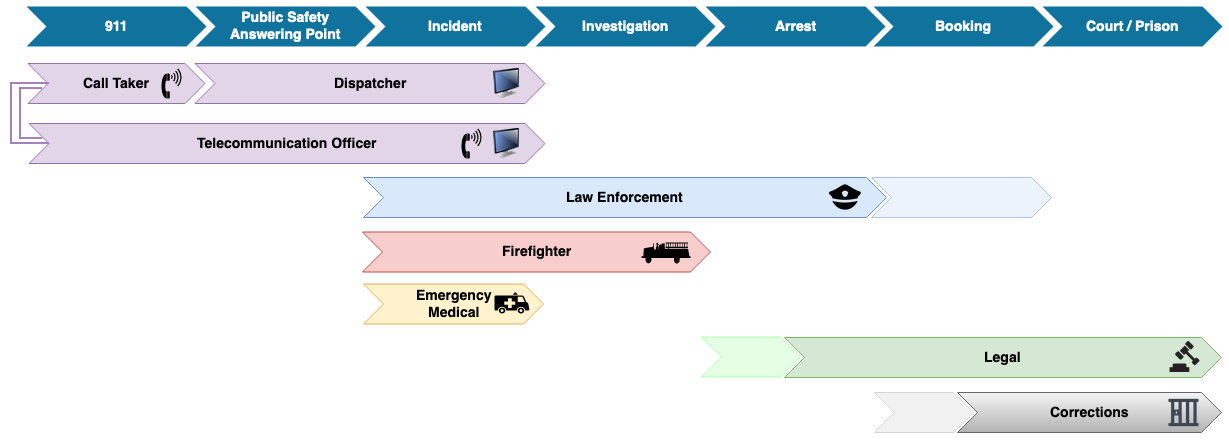
There are two things worth calling out here. First, there are two equal rows representing telecommunication officers. Dispatching often has workflows broken up among different parties because there are two kinds of PSAPs, primary and secondary. The 911 call goes to a primary PSAP first, but if that PSAP doesn’t dispatch that type of call, they will route that call to a secondary PSAP. For example, if an EMS call comes in but the primary PSAP only dispatches for LE, then a call taker in the PSAP routes the call to the secondary PSAP that gathers additional information and dispatches EMS responders. Those two models inform the workflow split or synthesis across call taking and dispatching. Second, the overlaps across roles are important to understand when looking at the value chain. The spots where information is consolidated and passed to the next responsible party are big software opportunities; the gaps are challenging and the likeliest places for mission critical mistakes.
To be clear, this is a highly abstracted look at a call for service. The intent is to give a sense of what the main buckets of work are. There are gaps, loops, and strange quirks all over the criminal justice system. Below is a flowchart from BJS that skims the early workflows during the CFS, but shows the intricacies post-arrest that I’m glossing over.

The Modern Duty Belt
Duty belts used to look like this:

Sparse. There’s a holster for a revolver, a dump pouch for additional ammo, a ring for a baton, and a clip to hold a set of handcuffs. Firearm, ammo, baton, cuffs. That’s it. Compare to today:

Today, it’s visually the same, but now it’s newer, tactical-er, and in the blackest matte on the market. On this belt from Ellenburg PD, there’s a Glock 22, 60 rounds of ammo, two sets of handcuffs, a Motorola two-way radio, a Taser, a MagLite, and a baton. This doesn’t even include a vest: many departments have added so much to the belt that it leads to ergonomic stress and back problems. The vest removes some of the jankiness of the belt, and allows for more gear.

Did someone say more gear? Fantastic. Now we can fit a bodyworn camera, pepper spray, and backups of whatever else couldn’t fit on a belt.
Although still recognizable, it’s clear that the duty belt has changed in appearance and use. This is just the tip of the iceberg. A casual observer has no idea the scale of change that an officer has experienced in the last 30 years. The modern law enforcement officer is now the human connective tissue between vast amounts of hardware and software. The technology stack augments officers with an improved ability to move, see, categorize, communicate, remember, and deliver force. Let’s look at the rest of the iceberg and define the Modern Duty Belt.
Hardware

The above diagram show what hardware is necessary and when during a CFS. Most are self-explanatory as categories, but a couple are not. In this context, Sensors include any static hardware that is distributed in a geographically strategic way to see or hear incidents while they’re happening (or play them back after). Shotspotter and Amazon Ring are good examples. LTE Devices is a purposefully ambiguous category, because the product category could play out in very different ways over the next decade. For now, it means connected devices like an agency-issued smartphone, or a Mobile Date Terminal (MDT) in the form of a ruggedized laptop or tablet in the patrol car. A Conducted Electrical Weapon (CEW) is a Taser.
Software

This diagram shows what software is necessary when during the life of a CFS. In this context, Cases are a court-specific definition and Investigations are what detectives work on. Many of these are in the process of bundling or un-bundling, which will make diving into their specific purposes, value propositions, and differentiation super fun.
Putting it together into one massive tech stack graphic:
Public Safety Stack

In future posts we’ll explore the value (and cost) of each tool, the companies that sell and service them, and how they’re adapting as society’s focus changes.
Thanks for reading. If you enjoy this newsletter, please share it, forward it to your friends, or just sign up here.
-MA
